Anatomy of a Domain Hijacking, part 1
Two weeks ago I'd never heard the term 'Domain Hijacking'. Right now, I'm in the middle of a fight to regain control of my hijacked domain, secretGeek.net. It's not an easy fight, I haven't yet won, and I may never win.
If you have any information that could help me get control of my domain again please leave a comment, or tweet me (@secretgeek), or get in touch via my (now re-secured) email address, leonbambrick@gmail.com
From Russia with Love
On Monday 9th May, I checked my gmail account at around 3:40 in the afternoon, and I was confronted with a dark red message at the top of the screen (in the area where you normally see messages like 'Your email has been sent'). The message said:
Warning: we believe your account was recently accessed from: Russia. Show details and preferences | Ignore
I clicked on 'show details and preferences', and a new window opened with this message:
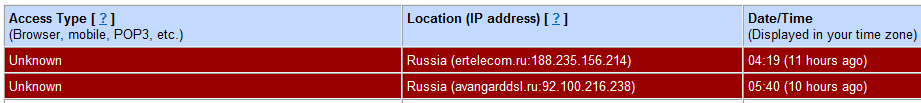
(click to see the message in context -- [note that my own ip addresses are redacted])
This was definitely not me. At 4:19 AM, and 5:40am I had been far too busy being fast asleep, preparing for a big week, to get to Russia and back for some casual email reading. So someone had infiltrated my email. The freaking out sensation began immediately. I couldn't move. I was frozen completely still.
I followed google's advice and immediately changed my password, then notified my wife. My mind was racing as to what the implications could be.
A little voice told me to check the trash. I was really hesitant, I think I knew the trash would contain something I didn't want to see.
In the trash I found two messages, received at 5:45am.
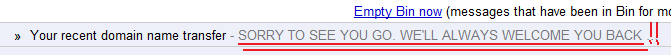
The content of the messages was to explain that my domain, secretGeek.net, had been succesfully transferred from my registrar, GoDaddy, to a Russian registrar, Regtime Ltd.
I felt completely unreal, like this was a dream, or a prank. I logged into my GoDaddy account to check on my domains. They all still appeared to be there. I took a few deep breaths. I felt it must be all just a daydream. I read the list carefully. No -- secretGeek.net was missing from the list. All of the others were still there.
I started sending emails to GoDaddy. I replied to the emails I'd found in the trash, telling them that it was a mistake, the result of my email being violated.
I lodged support requests with GoDaddy. When I went back to the trash to read the deleted emails again I found there were new messages in the trash. Emails from godaddy in response to my support requests had been automatically deleted. This was *weird*. It was a few minutes before the penny dropped.
I looked in my gmail filters and there were two new ones. The two new filters were designed to delete any messages containing the words 'GoDaddy' or 'Webnames'. (I later found that 'Webnames.ru' is the trading name of 'Regtime Ltd', the Russian registrar holding secretGeek.net)
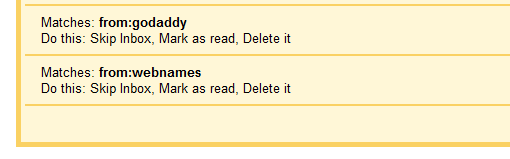
This was starting to become very 'real'. This wasn't some kind of misunderstanding. It was definitely a thing. It was a deliberate, targeted attack, by a person or people who knew what they were doing and had either done this thing before or had thought it through very carefully.
I turned to my friend, Joe Cooney, to show him what I'd found. He was equally gobsmacked. He told me to call GoDaddy on their support number and see what they said.
A whois request on secretGeek.net showed that my name servers were still listed, but the registrar was Regtime ltd, and the contact information was all blank.
The support guy at GoDaddy told me to contact the gaining registrar and find out what their policy is for transfer disputes. He told me there was nothing GoDaddy could do (turns out this was bad advice, by the way)
I was busy worrying about what else was in danger. My wife was already on the task of changing every password, keycode, and security question associated with all of our bank accounts, credit cards, online identities, home pcs etc, and checking at each of these places for any trace of unusual activity.
In order to send a support request to the Russian registrar, I had to sign up as a member (and I noted with some distaste that they sent me my new password in plain text.) I sent them multiple emails explaining what happened. Then I re-sent each of those messages, in Russian this time, translated by translate.google, and including the original text.
I worked late that day to make up for the lost time and somehow managed another check-in before I went home.
That night I called GoDaddy again, hoping to get more help. By now I'd read about the similar case of David Airey where a gmail vulnerability led to a domain hijacking, which also involved godaddy. This time I got a more helpful support staff member. She told me to fill out the 'dispute on transfer away' form at GoDaddy, which I promptly did. This meant that the right people at godaddy would be notified, and they'd contact the Russian registrar to request the domain be returned.
Wrapping up part 1.
While there's more that's happened since, things haven't really progressed since that day at all.
I still haven't regained control of the domain. I'm waiting on word from the Russian registrar. I remain hopeful that any minute now I'll get an email from them saying "Ah, we're sending back your domain!" -- but my hope is fading.
The name servers haven't been changed, so my content continues to be served up as always. If it does go down, the plan is to launch a new and improved secretGeek at LeonBambrick.com. Announcements or news will be via twitter (@secretGeek) or from my business website, NimbleThing.net.
If you have any information that could help me get control of my domain again please leave a comment, or tweet me (@secretgeek), or get in touch via my (now re-secured) email address, leonbambrick@gmail.com
In the next part of the story I want to discuss gmail security, all of the possible ways I could've been hacked, and the one I think is most likely. But I can't wait until then to put out the following checklists. These are steps that you can do to protect your email account and to protect your domains:
What can you do to stop this happening to you?
Protect your email via:
- Change your password often. For example, right now.
- Make your password very strong.
- In gmail: disable POP.
- Ensure your password recovery options are as strong as your password.
- Make sure 'always use https' is selected.
- In gmail: check for unusual activity (it's available at the foot of the screen).
- In gmail: don't let any other apps be associated with your account.
- Use two-step authentication.
Protect your domains via:
- Pay for private domain registration.
- Pay for enhanced transfer protection. (e.g. at GoDaddy they call it 'Deadbolt' protection, and it means they require you to send them identification before they'll approve a transfer.)
My book "Choose Your First Product" is available now.
It gives you 4 easy steps to find and validate a humble product idea.